Authenticate & admit
Only authorized webhook sources are accepted. Ingress policies validate authenticity before events enter the pipeline.
Deterministic execution, policy enforcement, agent control, and full audit trail — for Stripe, GitHub, Shopify, and every revenue-critical event pipeline.
Duerelay enforces correctness from ingestion to execution — preventing duplicate processing, enforcing policies, and recording every decision.
Only authorized webhook sources are accepted. Ingress policies validate authenticity before events enter the pipeline.
Policy gates enforce spend limits, throughput caps, and payload rules before any action executes.
Idempotent delivery prevents duplicates. Agent SDKs and bundles execute actions atomically with rollback on failure.
OTEL traces record every execution. Immutable audit trails and compliance export provide full accountability.
Per-agent credentials. Policy enforcement before execution. Atomic bundles with rollback. OTEL traces for every action. Give AI agents and automated systems access to webhook-driven actions with full governance and auditability.
Included on AI plansAgent SDKs provide a typed execute endpoint with per-agent credentials. Each agent operates under its own identity and policy scope.
Enforce spend limits, throughput caps, and payload validation before any agent action executes. Non-conforming requests are blocked with a clear reason.
Group multiple agent actions into a single bundle. If any step fails, preceding steps are rolled back automatically.
Require human approval before sensitive actions proceed. Every execution is recorded as an OTEL trace for full auditability.
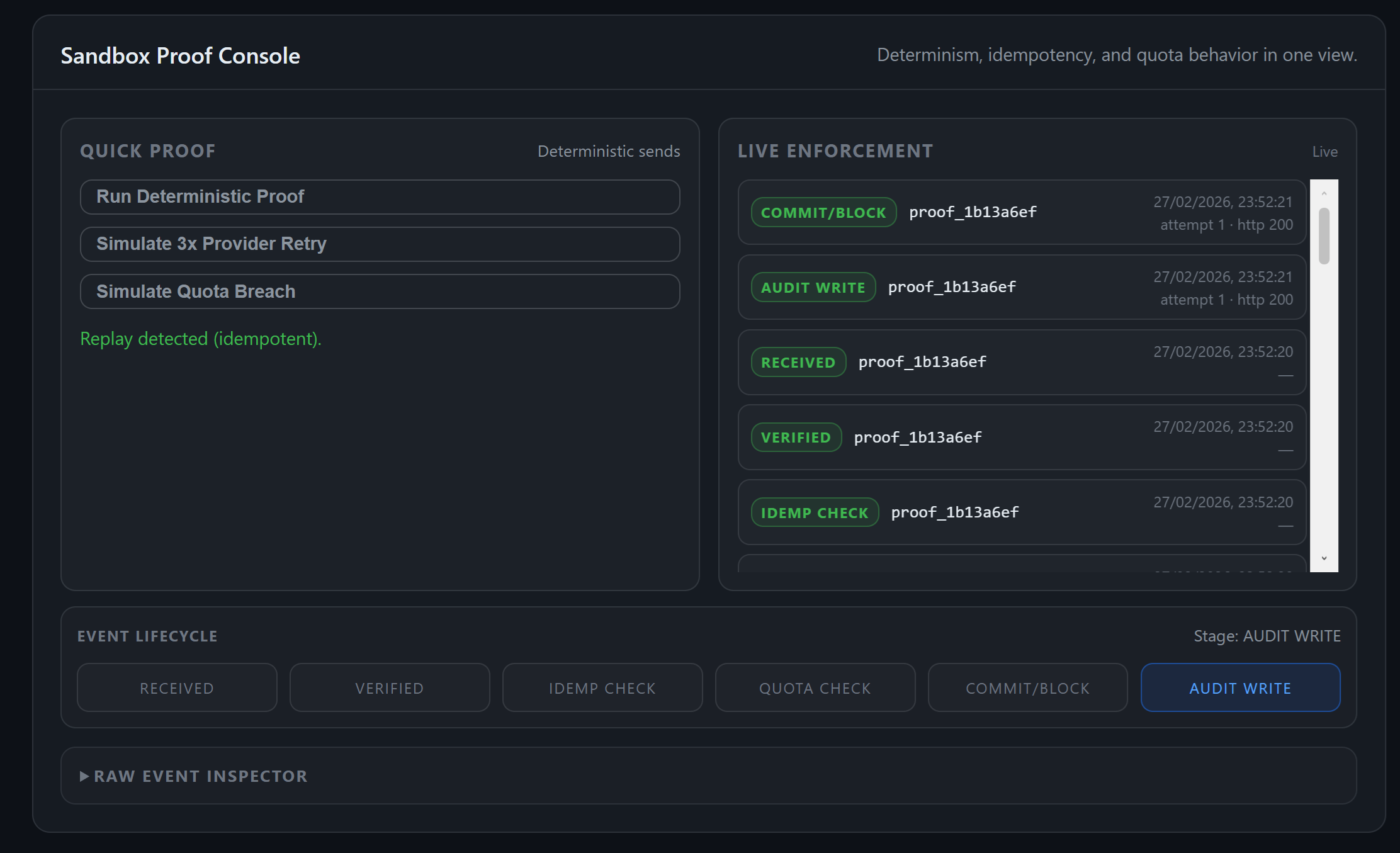
Developer tools for debugging webhooks, replaying failed deliveries, and endpoint health monitoring.
Inspect payloads and delivery attempts for every webhook event.
View tool →Retry webhook deliveries instantly to validate fixes.
View tool →Track every stage of webhook processing.
View tool →Detect failing webhook endpoints and delivery errors.
View tool →Evaluate webhook behavior in an isolated sandbox before relying on it in production.
Point your source at Duerelay, set a policy, and govern every event before it reaches your application.
Replace your endpoint URL with a Duerelay ingest URL. Works with Stripe, GitHub, Shopify, or any HTTP source.
# Stripe Dashboard → Webhooks → Add endpoint
Endpoint URL: https://ingest.duerelay.com/s/{your-token}
# Or register a source via API
curl https://api.duerelay.com/v1/sources \
-H "Authorization: Bearer dr_live_..." \
-d '{"name":"stripe","type":"stripe"}'Set budget limits, rate caps, and required fields. Non-conforming events are blocked before they reach your app.
{
"budget_eur_day": 500,
"rate_per_minute": 100,
"require_fields": ["customer_id", "amount"],
"block_on_violation": true
}Act on governed events from your app or an AI agent. Every call is idempotent, policy-gated, and OTEL-traced.
from duerelay.agent import Client
client = Client(agent_key="dar_live_...")
result = client.execute("process-payment", {
"order_id": event["data"]["id"],
"amount": event["data"]["amount"],
})
# idempotent · policy-gated · OTEL-tracedBilling, governance, and how Duerelay fits alongside other webhook tools.
Hookdeck and Svix focus on webhook delivery. Duerelay adds a governance layer on top: pre-execution policy gates (budget, rate, content), agent SDKs with per-agent credentials, atomic multi-action bundles with rollback, and OTEL traces — all enforced before any action runs against your application.
Every inbound webhook admitted through Duerelay counts as one event. Policy-blocked requests and sandbox traffic do not count. Overage above the plan quota is billed at €12 per block of 25,000 events. See pricing for plan quotas.
No. Gateway plans (Starter €19, Core €49, Scale €89) give you webhook delivery, replay, policy gates, and observability. The Agent Control Plane is included only on Agent (AI) plans and Enterprise, when you need typed agent SDKs, bundle execution with rollback, and approval workflows.
Yes. Every event retains its full payload and delivery history. Replays are instant, idempotent, and recorded in the audit trail — the deterministic execution layer prevents duplicate side effects even when the same event is replayed multiple times.
Any HTTP source. First-class integrations exist for Stripe, GitHub, and Shopify (including signature verification). Custom sources connect via a standard ingest URL with HMAC or Bearer authentication. See the quickstart for setup.
Public operational summary with no tenant identifiers.